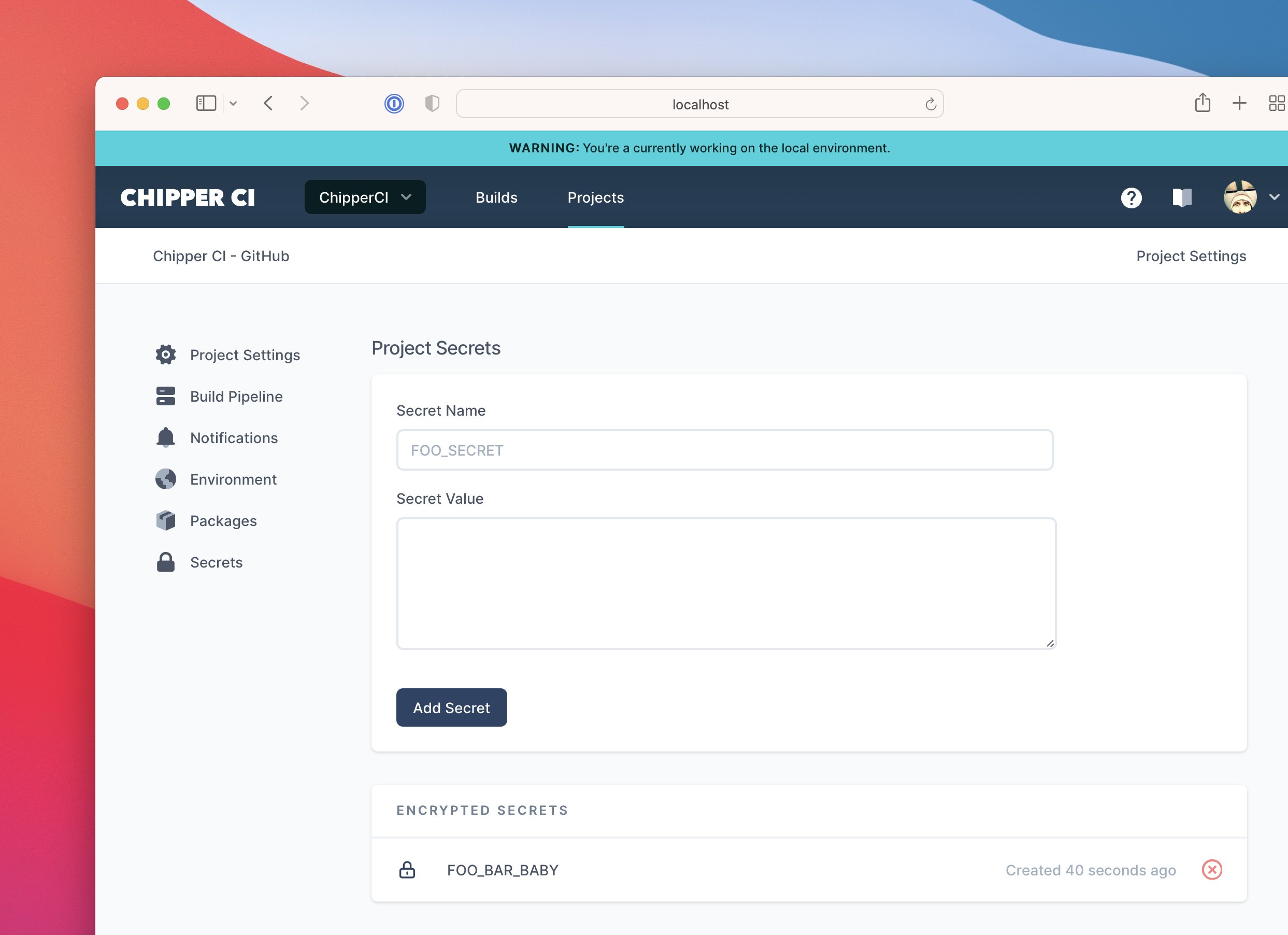
Secrets
Chipper CI can securely save sensitive data for use in Chipper's pipelines.
Secrets are encrypted. In fact, the raw values never reach our servers (an idea "borrowed" from GitHub).
Chipper CI, just like GitHub, is able to decrypt secrets, otherwise they'd be useless to you!
Using Secrets
Secrets can be added in two places:
- Team Settings - these secrets are available to every project in your team.
- Project settings - these secrets are specific to a project. Project secrets over-ride team secrets if they have the same name.
Secrets are exposed to your pipeline as environment variables. You use them in exactly the same way.
# Assuming DOCKER_USERNAME and DOCKER_PASSWORD are secrets
docker login -u $DOCKER_USERNAME -p $DOCKER_PASSWORDHiding Secrets
We take pains to make sure secrets are not leaked into your build output. Secrets that make their way into build output is redacted.
If you ever find secret values spilled into your build output, be sure to let us know!
